The Coding Manual for Qualitative Researchers
Coding examples from SAGE journals
Coding examples from SAGE journals providing actual examples of coding at work, giving you insight into coding procedures.
Included here are excerpts from seven Sage Publications journal articles that illustrate coding at work. They each provide an example of how researchers can document their analytic journeys for the benefit of readers. Read the full articles for more details on their coding procedures.
A coding snapshot
A simple half-page table with a list of codes and examples of related data can help readers get an idea of your methods as well as the participants’ perspectives. Snelson (2015) investigated school-related vlogging on YouTube. One portion of her study examined viewer comments posted online about other young people’s vlogs. “Of the 3457 comments, 53% were coded as positive, 12% were coded as negative, 29% were coded as neutral, and 6% were coded as mixed” (p. 335). The study “used comments as a reflective lens from the viewing audience to help illuminate vlogger culture and perhaps suggest additional motivations for vlogging, such as positive attention or community interaction” (p. 328).
Snelson’s use of Magnitude Coding is illustrated in the table below (p. 335). She provides the coding labels in the left-hand column and sample data that support the codes in the right-hand field. This snapshot provides readers concrete examples and possible future guidance for comparable analytic work.

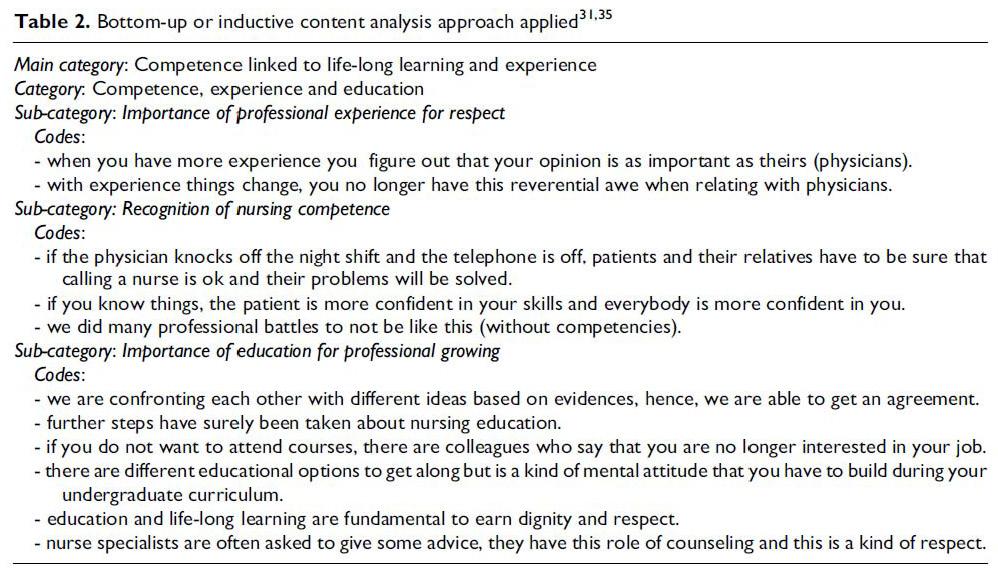
A category and codes snapshot
Readers can benefit from seeing how codes become organized under broader categories. A simple half-page table with a list of codes and their categories illustrates a portion of the analytic journey. Stievano, De Marinis, Russo, Rocco, and Alvaro (2012) analyzed nurses’ professional dignity. Focus group interviews were transcribed and meticulously analyzed, “identifying codes, sub-categories, categories and thematic areas” (p. 345). The researchers explain that
the textual units (codes) were sorted out, summed up and categorized. Subsequently, open codes with similar content were arranged in sub-categories and then categorized. The categories were identified around different meanings of nursing professional dignity in community and hospital settings. All main categories were then compared and two main themes on professional dignity emerged. (p. 345)
The table below (p. 345) illustrates one example of a category, its subcategories, and their related “codes” – in this case, extended participant quotes. This snapshot provides readers an analytic example of how codes are subsumed into subcategories, which are then in turn subsumed under a larger category label.
A coding protocol
Readers may wish to have more detailed information about a study’s coding procedures or its protocol. Even a simple listing or hierarchical/organizational outline of codes can provide a sense of the overall analytic scheme and a holistic review of results.
Fletcher and Blair (2014) conducted individual interviews with adolescents about their parents’ rules for cell phone and social media use. The codes were inductively generated from the transcript data and “modified through an iterative process wherein coders engaged in multiple independent readings of these transcripts, meeting in pairs between each round of readings to add codes, delete codes, or clarify code definitions so as to accurately reflect adolescents’ descriptions” (p. 6). The resulting protocol, below, is presented as an appendix to the report (pp. 17–18).
Appendix 1
Final Codes Related to Cell Phone Use (Parallel Version for Use of Social Networking Sites)
1. Proficiency with cell phones compared with parents
(a) Perceived proficiency
- Teen perceives self as more proficient
- Teen perceives self and parent approximately equal
- Teen perceives self as less proficient
(b) Example type
- Teen demonstrates more knowledge or use than parent
- Parent demonstrates more knowledge or use than teen
- Expression of teen’s own confusion/difficulties
- Expression of parent’s confusion/difficulties
- Discussion of use of specific functions or usage patterns
- Parent has access to technologies but does not use them or uses them in a limited way (e.g., has texting function but does not text, has a Facebook but only reads what is written on wall)
2. Type of rule parents have for cell phone use
- How much time can be spent on phone
- When or where phone can be used
- Who phone can be used to communicate with
- Number of minutes or texts that can be used
- Content of communications
- Take good care of the phone itself
- Rules regarding what adolescents have to do to have cell phone privileges or what behaviors can result in loss of cell phone privileges
- No explicit rules
3. Why parents have a rule or rules
- Safety concerns
- Morality concerns
- Financial concerns
- Cell phones are a privilege or parents have the right to control their use
- Concerns about teen’s physical, emotional, or social well-being (e.g., needs sleep, needs uninterrupted dinners, a trust issue, academic concerns)
Narrative descriptions of coding
There are times when a detailed explanation of a coding procedure is necessary to clarify the analytic approach or to describe problematic issues. Cannon (2012) employed Dramaturgical Coding for her analysis of an interview transcript about an English language learner at a community college. The article features detailed descriptions of her analytic processes leading to the final product – an ethnodramatic play script that dramatizes the international student’s story. But Cannon first explains how the microanalysis of data provided her foundations for later coding cycles and eventual development of the drama. The article is a masterful behind-the-scenes account of how a coder wrestles with data and exploratory methods. Below is the beginning of that confessional tale (p. 585):
First-Round Coding: Dramaturgical Coding
To code the data, I reread the transcript of the interview and used Saldaña’s (2009) dramaturgical coding, in which lines are coded, using a combination of in vivo and gerund codes. In addition, each coded line is assigned a secondary code in order to reveal the perspectives, motives, and conflicts of the participant. Saldaña borrows this coding system from Bogdan and Biklen’s strategy codes. This system employs six codes: Objective (OBJ), Conflict (CON), Tactics (TAC), Attitudes (ATT), Subtext (SUB), and Emotions (EMO). To illustrate one example, the following line from Edem’s interview would be coded as follows.
And I can say that some advisor helped me. And most of the clerical person help me. And they. It was very interesting. It’s not like my country. You have to give something like a money [bribe].
Codes:
ATT: Americans as helpful
EMO: grateful
As I read and coded line by line, I felt that the coding scheme seemed simultaneously inductive and deductive, a combination that Denzin (1978, cited in Patton, 2002) might call abductive. That is, I could name the codes as I felt appropriate, but I also had to deductively decide how these codes fit into predetermined secondary codes (e.g., emotion, subtext, etc.). Two key issues arose: (a) Some lines did not conform to a single code, and (b) the processing of coding for emotions and subtext – which often required my remembering Edem’s vocal expression or
tones, or to recall the meaning laden silences between question and answers – proved to be difficult. To address the first issue of overlapping code, I often coded one sentence with several codes, as in the case below.
I am going to school because I think I need the basics. Help you to do something.
Codes:
SUB: needing the basics
OBJ: getting a job
Codes and categories in diagrams
Diagrams of codes and categories (or concepts, themes, etc.) are particularly useful when processes of human action are involved, or the complexity of the analysis necessitates graphic representation, such as networks, to support the explanatory narrative. Togia, Korobili, Malliari, and Nitsos (2014) investigated the perceptions of secondary education teachers about their students’ information literacy skills. ATLAS.ti software was used to analyze the interview data and create several diagrams for the co-authors’ published report.
The co-researchers’ diagram below illustrates the information-seeking behavior of the adolescents. “The number and types of sources students consulted depended on the assignment they had to hand in and the directions they received from their teachers. … It seems that many of the respondents tried to draw students’ attention to both print and electronic material, but in most cases the Internet prevailed” (pp. 7–8). The diagram also serves as a general outline for the discussion of each bin, supported with participant quotes or vignettes. This “analysis at-a-glance” provides readers a holistic grasp of interrelated facets of a study, and enables them to see the relationships and processual flows of codes, categories, themes, and concepts constructed by the researchers.

Mapping the analytic journey
When possible, researchers should describe or illustrate their process of transforming codes into their consequent analytic products (e.g., major themes/concepts, key assertion, theory). A brief description of the journey from beginning to end, especially if it can be shown on just one page, helps readers see the big picture.
Brooks (2015) studied school principals in Southern Thailand working in tension-filled communities and utilized for her data analysis a “conceptual framework that conceived of trust as five interrelated constructs: benevolence, honesty, openness, reliability, and competence” (p. 232). The five constructs served as a priori codes that helped formulate more detailed codes and thus categories and thence into themes. Her one-page diagram of the entire analytic process, below, is an elegant overview of how one begins and progresses toward condensation and summation of data (p. 240).

Abbreviated codebooks
As publishing space permits, authors may wish to include an abbreviated codebook as an appendix to their reports. This provides readers not only an author-initiated audit of the coding and analytic processes, but also a possible template for Protocol Coding by other future researchers investigating comparable topics.
McHugh, Horner, Colditz, and Wallace (2013) explored “adolescents’ perceptions of the bridges that foster and the barriers that inhibit supportive relationships with teachers, and the boundary expectations that function as both” (p. 9). Their Descriptive and Structural Coding approaches were applied to focus group data, and the co-authors provide a meticulous account of their procedures and how they resolved co-occurrence coding dilemmas. They explain that Structural Coding, in particular,
deliberately labeled the perceived effect of the interaction on the closeness of the interpersonal relationship. As such, we were able to explore the driving question in this coding process, “Did the interaction bridge the two people to bring them closer together, or did it separate them or create a barrier between closeness developing?” Finally, by examining the thematic patterns identified, we gained a full understanding of the processes that the participants related to us. (p. 18)
Below is the abbreviated codebook from the co-authors’ study (pp. 35–8), a rare form of appendix in journal articles.
Appendix
Abbreviated Codebook
Barriers
Back-Channel Communication: incident in which two or more people are talking about another; most frequently, topic person is not present (though this may occur), and such communications are inferred by or later related to topic person.
Boundaries: participant expresses that someone is expected to act or speak in some way based on rank, role, or relationship.
Carelessness: instances or occurrences in which the participant or the person about whom the participant is relating failed to adequately take into consideration another person’s needs, desires or likes/dislikes; may refer to verbal, physical, engagement, emotive, or relational.
Consequence: a repercussion of a given action, behavior, statement or incidence.
Inattention: instances or occurrences in which the participant or the person about whom the participant is relating failed to adequately attend to another person’s actions or communicated thoughts or feelings; may refer to verbal, physical, emotive, or relational.
Stereotype: when a person is presumed to behave, believe, think, or experience some emotion simply because of some external categorization; typified by an intensified, overgeneralized, and frequent reinterpretation of a perceived attribute to an extreme degree and applied regardless of contrary fact/observations.
Unspecified Barriers: processes which act as barriers to a relationship growing closer, but that do not meet the definitional criteria of another specific barrier process.
Bridges
Connecting: participant refers to or describes the process by which someone transitions into “being known” by the participant, or by which the participant is “known” by them; the act of connecting with another person, or growing closer.
Effortful Engagement: an instance in which one person actively and deliberately engages another on an interpersonal level.
Help-Seeking: the act of requesting and/or receiving assistance from another person; may be educational, verbal, financial, physical, or advisory; the request for one to enact one’s resources for the benefit of another.
Personal Disclosure: participant describes or relates an occurrence in which they either shared something personal with another person, or when another person shared something personal with the participant; may be positive, neutral, expression of uncertainty or vulnerability, or any of these in combination with negative.
Prediction and Interpretation: when a person demonstrates the ability to anticipate another person’s reaction (verbal, active, emotive, etc.) to an action (verbal, active or emotive) performed by the predictor, and to accurately gauge their intention underlying communication, actions undertaken, etc.
(Understanding) Constraints: temporal, monetary, physical, familial/relational, etc. features of a participant’s life which, per participant report, may make connecting to others or completing a given task a more complicated and/or difficult proposition than would otherwise be.
Support
Unspecified Support: the act of providing or sharing emotional assistance, reassurance or bolstering, or other form of support that do not meet the definitional criteria of another specific support process.
Catharsis: mutual emotion sharing or emotional expression between two or more persons.
Companionship: the desire to share time, physical space, or communication with another person, typically in a friendly or emotionally positive manner.
Conflict Resolution: the act between two or more people to work collaboratively on resolving a point of disagreement, conflict, misunderstanding, etc.; primarily verbal, though may incorporate resource allocation.
Empathizing: an attempt to share in or recreate another’s emotional experience.
Leniency/Willingness to Work Out Difficulties: the emotional and cognitive intention and commitment to resolving conflicts, differences of opinion, etc. that occur between two or more persons; this implies the intention to apply effort.
Problem Solving: request and/or receipt of assistance from one person by another in dealing with a real or hypothetical problem, conflict, tumultuous situation, or issue; primarily verbal in nature, and tends to be focused on social situations or circumstances.
Protection: the act of buffering or guarding another person; may be verbal (e.g.: verbal defense), physical, legal, or emotional/relational.
Resource: various different types or degrees of assistance that one person can or does offer another person; may be financial, emotional, temporal, protective, work/education, etc.
Sharing of Difficulties: discussion of the revelation of personal problems, concerns or issues to another person; participant may be discloser, or disclosed-to, but specific subject matter regards a negative occurrence in the discloser’s life.
Soothing: the desire of a person for the consideration, kind words, or soothing actions of another person; the act of providing the above.
Structural Codes
Teacher Does: incidents in which a participant relates a specific instance or example of behavior that was specifically done by the teacher.
Teacher Does Not: incidents in which a participant relates a specific instance or example of behavior that was specifically NOT done by the teacher; these incidents are most typically paired with a value-judgment.
Teacher Should: incidents in which a participant relates a specific instance when they feel that a teacher SHOULD have done something (coded regardless of actual occurrence of the behavior), or example of (potential or actual) teacher behavior that the student relayed feelings (or an affirming value judgment) that such behavior SHOULD happen.
Teacher Should Not: incidents in which a participant relates a specific instance when they feel that a teacher SHOULD NOT have done something (coded regardless of actual occurrence of the behavior), or example of (potential or actual) teacher behavior that the student relayed feelings (or a negative value judgment) that such behavior SHOULD NOT happen.
References
Brooks, M. C. (2015). School principals in Southern Thailand: Exploring trust with community leaders during conflict. Educational Management Administration & Leadership 43(2), 232–52.
Cannon, A. (2012). Making the data perform: An ethnodramatic analysis. Qualitative Inquiry 18(7), 583–94.
Fletcher, A. C., & Blair, B. L. (2014). Implications of the family expert role for parental rules regarding adolescent use of social technologies. New Media & Society. doi: 10.1177/1461444814538922.
McHugh, R. M., Horner, C. G., Colditz, J. B., & Wallace, T. L. (2013). Bridges and barriers: Adolescent perceptions of student-teacher relationships. Urban Education 48(1), 9–43.
Snelson, C. (2015). Vlogging about school on YouTube: An exploratory study. New Media & Society, 17(3), 321–39.
Stievano, A., De Marinis, M. G., Russo, M. T., Rocco, G., & Alvaro, R. (2012). Professional dignity in nursing in clinical and community workplaces. Nursing Ethics 19(3), 341–56.
Togia, A., Korobili, S., Malliari, A., & Nitsos, I. (2014). Teachers’ views of information literacy practices in secondary education: A qualitative study in the Greek educational setting. Journal of Librarianship and Information Science. doi: 10.1177/0961000614532485.
